Apps have taken over the world. It is not an exaggeration, just a fact of modern-day life. We have apps that help us shop, order food, monitor our health and even control the temperature of the air-conditioner in the room! But perhaps, the most important apps we use are payment applications. Digital money has transformed our lives for the better. Your smartphone is now your wallet and much more.
Have you ever wondered what it would be like to use an app that controls your life? Apps are everywhere these days. If there’s something we want but don’t have access to, either because of where we live in this world OR our wallets aren’t deep enough. One popular type of application out right now is the payment application. which lets users send money remotely without having any transactions fee hooked up.
It’s time to put your money where the mouth is if you want a successful app. With so many runners in this field, it can be difficult for new players like yourself who are looking at venturing into developing their own secure payment apps and replacing cash-in-hand commerce with them – but don’t worry! there are a few items that you need to tick-off from your list if you want to develop your own secure payment app.
Here is the checklist to creating a secure and safe payment app:
The PCI:

The Payment Card Industry Security Standards Council (PCI SSCC) was created by international payment network heavyweights including Visa, MasterCard American Express Discover JCB in 2006. The goal of the council is to create standards that prevent credit card fraud and provide protection for consumers worldwide who use these cards online
PCI-DSS 4.0, the latest version of the Payment Card Industry Data Security Standard, is expected to be released in Q1-2022. Like all versions of PCI-DSS, 4.0 will be a comprehensive set of guidelines aimed at securing systems involved in the processing, storage, and transmission of credit card data.
PCI-DSS applies to any organization that processes, stores, or transmits cardholder data (or that provides services that control or could impact the security of cardholder data or the card holder data environment). To comply, organizations need to fulfil a variety of requirements; these include ongoing monitoring/testing, implementing strong access control measures, protecting cardholder data, and more.
Although the full text of PCI-DSS 4.0 has yet to be released, we do already know a fair bit about it. The PCI Security Standards Council (the organization responsible for PCI-DSS) has set four objectives to guide the creation of Version 4.0
Read on to find more on PCI-DSS
Third-Party Payment Gateways:

Payment gateways are an important part of a good application. They act as digital terminals, processing credit/debit card data and transmitting it to the processor for verification before deducting funds from your account or charging interest on any remaining balance if necessary.
The most common choice for small businesses is a full-stack payment platform, which offers more features than just basic transactions. These platforms offer an all-in-one payment gateway along with processor and merchant account service. Another benefit of using these platforms is that they handle and store data on behalf of the merchants. This lowers liability and makes PCI compliance possible.
However, third-party payment gateway platforms carry monthly fees and may take a share from every transaction made. Selecting a platform that caters to the needs of your business model and payment app objectives is crucial.
Network Tokenization:

What is Tokenization? Simply put, it is the process of replacing sensitive data with non-sensitive equivalents. This is often done to improve data security. In the payments industry, tokenization is a term used quite frequently. You may have heard of services like Apple Pay and Android Pay. These platforms use tokenization as a way to keep your card information safe when making a purchase. Let’s take a closer look at what Network Tokenization is and how it can benefit you!
The constant fear of hackers and malware make it a major concern while working on the internet. To safeguard themselves, many card networks like Visa have taken steps towards tokenization which converts sensitive data from your credit or debit cards into an encrypted form that cannot be used without permission by those who possess it but still lets users use their own money as usual at stores just like you would with any other plastic wallet! A token is then created by the service provide that takes the place of the PAN partially or wholly. A token generally contains randomly generated numbers or symbols, which is viewed by the merchant throughout the transactional process.
Tokenization is a great way to prevent information security breach by replacing actual data with temporary or dead data that cannot be utilized further.
Conduct Penetration Testing:
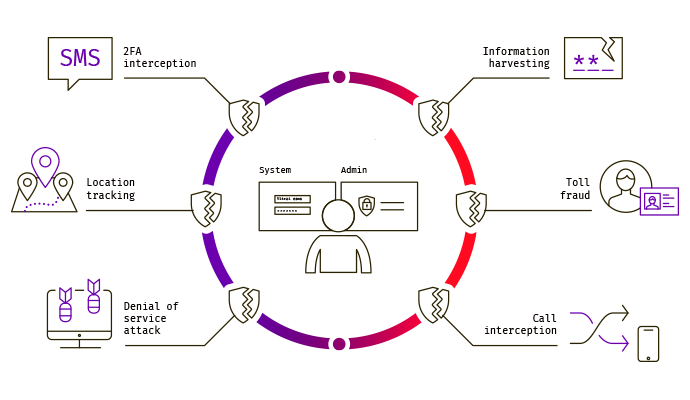
Once your payment app is ready, it needs to be tested. Technology gets better once limitations and loop holes are recognized and dealt with. It is all the more important for payment apps as any breach in security can likely compromise user data and grant access to the user’s monetary accounts. Conducting penetration testing by means of ethical hacking can help test the defenses of the application and figure out if there are any security patches that are vulnerable to compromise. Thorough testing is the only way to strengthen an application’s security framework.
It is no secret that the world of e-commerce has grown exponentially over recent years. As a result, so too have security risks and breaches associated with it – something which cannot be ignored by either consumers or retailers alike if they hope to maintain business volumes going forward into 2022+
The internet isn’t perfect; there will always exist vulnerabilities due both external ( hackers ) attacks on your website as well any bugs within its code itself . To truly protect yourself from being hacked while online shopping , you should make sure all applications used in conjunction are secure beforehand.